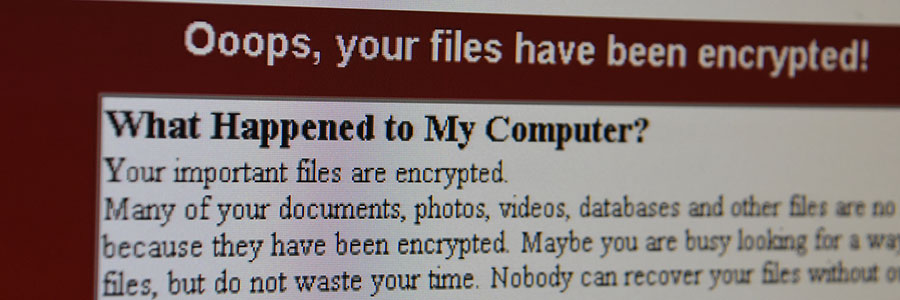
A new, Locky-type ransomware is currently infecting tens of thousands of computers worldwide. It uses the same code from the 2016 version to encrypt users’ files and it looks poised to cause another massive cyber emergency. Here’s everything we know so far.
It’s time to redefine the word “hacker”
Steer clear from these types of malware
Beware: Nyetya is worse than WannaCry
Worrying evidence of poor router security
PC fixes are a drain on your company’s budget

Security professionals should be beefing up your network security, implementing advanced firewall software, and identifying risks for possible breaches. In reality, they spend a huge chunk of their time troubleshooting issues on individual personal computers (PCs). That workflow is not ideal, but that’s what normally happens in many organizations.
Lessons learned from the WannaCry malware
This fake Google app is really a phishing scam
Sly phishing attack catching users off guard
You pay close enough attention to the links you click to avoid clicking on something like goolge.com or evrenote.com...right? Because if you’re not, you could end up exposing your computer or smartphone to a host of malware. The newest phishing attack strategy is the worst of all, and can catch even the most astute users off guard.
Wikileaks’ charges of government spying
Staving off malicious cyber attackers is already a herculean task, so the last thing you need is to feel exposed from a totally new angle. That’s how many felt after Wikileaks’ accusations that the US government was spying on its citizens. However, the truth is a lot different from what the headlines would have you believe.